You may be expected to supervise changes to live environments, with responsibility for IT security. You may also have a role in ensuring your organisation conforms to any new standards. Training your systems users may also be necessary, along with the creation of documentation supporting both new and existing systems. You may be responsible for designing, testing and Implementation of IT Security solutions as well as on-going maintenance and monitoring of live production environments. This can take the form of other, related work experience, or it can take the form of a structured internship or other formal hands-on learning. ASML is an Equal Opportunity Employer that values and respects the importance of a diverse and inclusive workforce. We recognize that diversity and inclusion is a driving force in the success of our company.
These professionals work on investigating cyberattacks, determining what caused them, and how exactly the network or computer system was infiltrated. Their primary role is to simulate a cyber attack to test their clients’ various security programs and firewalls.
he Always Encourage Us Towards Our Task And Good Learning Sources For Project Management
Planned security for special and high-risk events Identified, investigated, and resolved security breaches. Provided communication between officers and emergency responders during critical and non-critical emergency events from report to resolution.

You may need to provide an initial incident response together with problem solving as new IT Security related issues develop. The work may involve maintaining security software and integrating new security into an organisation using various tools and techniques including firewalls, spyware, malware detection and intrusion detection systems. The professional must keep themselves updated with the new trends and procedures.
Cybersecurity Specialist Employment Outlook
The fact that more and more businesses are relying on cloud computing, technology, and remote work presents further reasons to prioritize security infrastructure. You may be expected to provide production support to all live environments. You will be using your knowledge of IT security, authentication, session and communication protocols and general awareness of the environments at your organisation to get your job done. The installation and configuration of firewalls and other intrusion detection systems might be part of your role.
- Many students come to Fox Valley Tech with credits they’ve already earned, either while in high school or at other colleges and universities.
- Information Security, 5%Developed and distributed information security-related guidelines and procedures.
- Your role may involve liaison with all system users affected by the project.
- Have strong interest in cybersecurity regulatory rules, requirements and enhancement.
Some jobs you might find interesting include a Patrol Officer, Enforcement Officer, Protective Officer, and Public Safety Officer. Test CCTV, access control, intrusion detection, and area illumination systems for operational effectiveness, vulnerabilities, and reliability.
Pluralsight Courses & Certification Prep
You might receive job training if the employer has several bodyguards or a personal security team. Postsecondary education in criminal justice or police science can be beneficial. Square builds common business tools in unconventional ways so more people can start, run, and grow their businesses. When Square started, it was difficult and expensive for some businesses to take credit cards. Square made credit card payments possible for all by turning a mobile phone into a credit card reader. Since then Square has been building an entire business toolkit of both hardware and software products including Square Capital, Square Terminal, Square Payroll, and more.
- Security related deployment, on-going support, user training and perhaps documentation of new processes, procedures and applications may also be part of your job role, all depending on your organisations requirements of you.
- Those security specialist jobs related to physical security may include couriers, on-site security, or personal bodyguards.
- They install, program, and maintain automated systems, including managing the distribution and coding of security passes or ID cards.
- In addition, the program requires the completion of a traditional group of general education courses.
- This program provides students with entry-level skills for a profession in network security.
A security specialist must have a strong command of programming languages and system codes, as well as broad experience with technical expertise. Industrial security specialists develop, implement, and manage security systems and procedures for a variety of industries including manufacturing, information technology, and the military. They collaborate with security officers, perform regular security inspections, and resolve any security risks or threats.
What Does A Cyber Security Specialist Do?
This program is designed to provide a comprehensive program to develop a skilled workforce in the emerging field of information technology security. Managing information security programs consists of preserving information confidentiality and protection, risk management, data and system integrity, availability, authenticity, and utility.
Other vocational choices include armored car guard and gaming surveillance officer. If you’re in the former career, then you’ll work with banks to transport and protect money as it’s transported from one location to another. If you’re involved in the latter occupation, then you’ll help protect casinos during monetary exchanges. You will define policies, processes and guidelines to ensure compliance with global privacy and security laws and regulations . Additionally, we consider qualified applicants with criminal histories for employment on our team, assessing candidates in a manner consistent with the requirements of the San Francisco Fair Chance Ordinance. Based on 110 responses, the job of Information Security Specialist has received a job satisfaction rating of 3.89 out of 5. On average, Information Security Specialists are highly satisfied with their job.
Security Specialist Overview
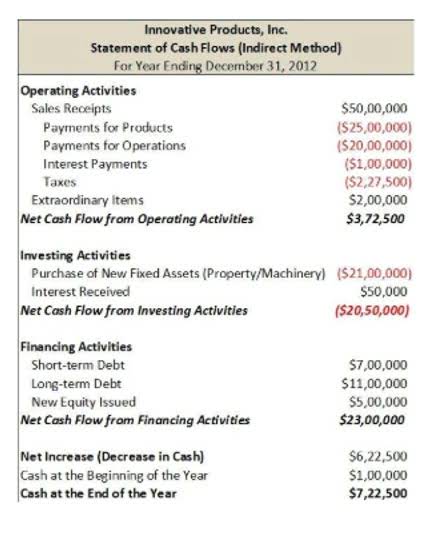
It is really a job description covering many of the tasks within many and varied entry to intermediate level IT Security job roles. According to ZipRecruiter, the Cyber Security Specialist salary is $107,433 per year in the United States. As per Glassdoor, for this position, the professionals earn about $67,620 per year. The Indeed salary estimate states that the Cyber Security Specialist salary is $113,483 per year in the United States. The US Bureau of Labor Statistics, the wage of Cyber Security Specialist, is $90,120 per year.
- The fact that more and more businesses are relying on cloud computing, technology, and remote work presents further reasons to prioritize security infrastructure.
- As with most jobs, earnings are influenced by a number of factors and can vary widely.
- The certification covers topics such as architecture, engineering, and management.
- “We’ve never had a three-month period with a loss or decline in premiums for IT security specialists.”
They must have a thorough understanding of computer programming, and they should be trained in risk management. Computer security specialists must also be able to communicate technical information clearly and concisely. As computer networks grow and more sensitive data is stored on computer files, the need for trained, skilled computer security specialists will also grow. Computer security specialists help businesses, educational institutions, and government organizations to control access to their computer networks and protect important data stored there. A security specialist, also known as an IT security specialist or a cyber security specialist, is responsible for developing and implementing security measures for an organization. As a security specialist, your overarching goal is to analyze current security procedures and suggest changes to upper management for improving efficiency and overall security.
Analytical skills have to do with gathering information from various sources and then interpreting the data in order to reach a logical conclusion that benefits the business. Lead TPS team by example through training and on job situations and coaching and corrective action. Process a variety of NCIC queries and provide timely response as appropriate or require. Managing, coordinating, and supervising all security operations, protocols, and processes. We believe in being fair, and are committed to an inclusive interview experience, including providing reasonable accommodations to disabled applicants throughout the recruitment process.

They are also responsible for anticipating future threats and advising on how to deal with them. The Security Specialist conducts threat and risk analysis and provides essential suggestions. The professional help in performing research, testing, evaluation, and deployment of security procedures. The specialist design https://remotemode.net/ security training materials and organizes training sessions for the other departments. They take care of network traffic and internet connectivity data and reports on risks. Cyber Security Specialist is responsible for providing security during the development stages of software systems, networks and data centers.
They look for security breaches launched through removable media , web and email attacks, loss or theft of devices, unauthorized use of system privileges and attacks on encrypted data. A computer security specialist may work onsite or remotely, depending on the company.
Computer security specialists also implement application access controls, such as password authentication, that keep unauthorized users from accessing a particular computer or network or program. Computer security specialists take steps to deny hackers access to a system and set up programs that detect hackers who do intrude onto a system. Computer security specialists also may be responsible for controlling site-specific physical access to computers. Coursework or a degree in computer science, computer engineering or electrical engineering can get you started. You can pursue courses in cybersecurity, beginning with Cisco’s free “Introduction to Cybersecurity.” As you gain more education and earn more certifications, you’ll have more employment and salary opportunities. They are responsible for making sure that networks and computer systems are up-to-date and not vulnerable to software bugs. One of the primary responsibilities of a cybersecurity specialist is to keep tabs on the systems employed by their organization and report any issues to management.
One of the top online resources for cybersecurity job seekers and those interested in pursuing a career in information security is CyberSeek.org. On its how to become a security specialist Career Pathways page, CyberSeek lists Cybersecurity Specialist/Technician as an entry-level position (one that pays an average salary of $92,000).